Kubernetes Networking Tools: A Layer-by-Layer Guide to What Fits Where
Stop getting lost in the K8s networking soup. Learn exactly how traffic flows and where tools like Ingress, CNIs, and Service Meshes actually fit in.
If you are in the DevOps world, especially the Kubernetes world chances are you have heard a lot of buzz around Kubernetes networking tools. And recently, with the announcement around NGINX Ingress deprecation, you might be seeing even more discussions on social media about alternatives, new tools, and opinions flying all over the place.
But if you are someone like me, you might have paused for a second and wondered:
“Wait… what exactly are all these tools?”
“Where are they actually used?”
“Why do we even need so many networking components in Kubernetes?”
Trust me, I had the exact same questions.
At first, terms like Ingress, Gateway API, CNI, Service Mesh, Cilium, Istio, Envoy, MetalLB, and Load Balancer can feel like a giant networking soup 🍜.
But here’s the interesting part: Most of these tools are not competing with each other. Instead, they solve different networking problems at different layers of Kubernetes.
So in this blog, we are going to take a fun and practical deep dive into:
✅ Kubernetes networking basics
✅ What happens when traffic enters a Kubernetes cluster
✅ Which networking tools are used where
✅ When to use what (without getting confused!)
By the end of this blog, whenever someone mentions a Kubernetes networking tool, you should be able to say:
“Ah okay, I know exactly where this fits in.”
So grab your coffee ☕ (or tea 😄), and let’s get started.
The Basics: How traffic flows in Kubernetes ?
Before we start throwing around fancy names like Cilium, Istio, Gateway API, Envoy, MetalLB, or Service Mesh, let’s first understand something important:
How does a normal request travel inside Kubernetes? Because once we understand the journey of a request, understanding networking tools becomes much easier.

When a request comes from the internet to your application running inside Kubernetes, it goes through multiple layers before reaching the actual Pod.
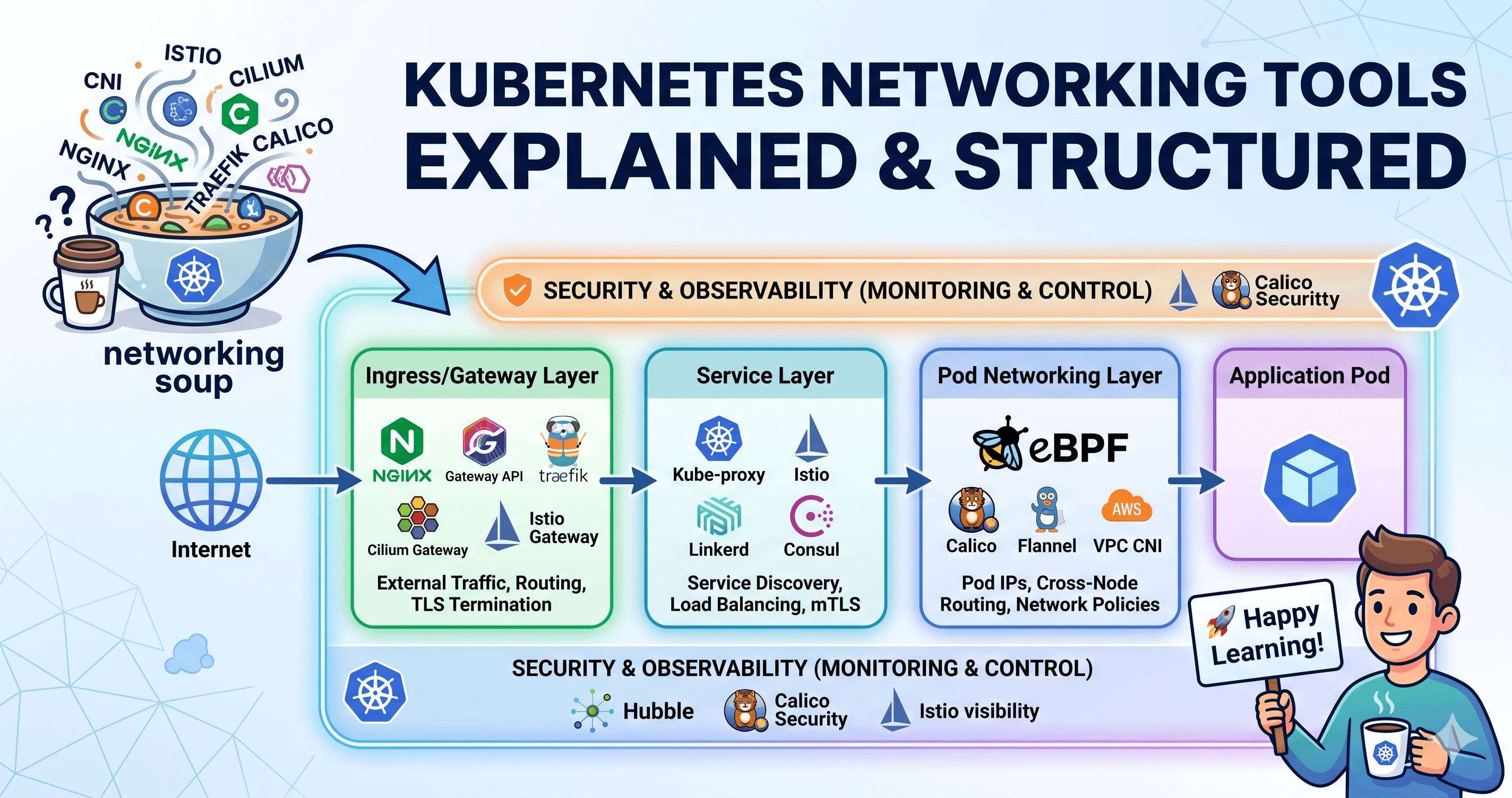
A request flowing inside Kubernetes typically goes through the following stages:
Internet → Ingress / Gateway Layer → Service Layer → Finds the Correct Backend Pod → Pod Networking Layer → Delivers Traffic to the Pod → Application Pod → Serves the Request
The request originates from an external user or application. For example: https://myapp.com
At this point, Kubernetes needs a way to expose your application to the outside world. So the traffic enters the cluster through the:
Ingress / Gateway Layer
Ingress / Gateway Layer → Controls External Traffic.
This layer acts as the entry point of the cluster.
Here Kubernetes decides:
Which application/service the request should go to URL/path-based routing (/payment, /user, /orders)
Authentication and authorization
TLS/HTTPS termination
Rate limiting and traffic filtering
Once the request rules are evaluated, the traffic is forwarded to the:
Service Layer
Service Layer → Finds the Correct Backend Pod
Services act as a stable endpoint for Pods. Since Pods are temporary and their IPs can change, Services help Kubernetes reliably find the correct application Pods.
Here Kubernetes:
Finds matching Pods using labels
Performs load balancing Routes traffic to healthy Pods
Enables service-to-service communication
Once the correct Pod endpoint is identified, traffic is forwarded through:
Pod Networking Layer
Pod Networking Layer → Delivers Traffic to the Pod
This is where the actual packet routing happens. The networking layer ensures Pods can communicate: Within the same node, Across different nodes, Across namespaces, Across the cluster.
Here Kubernetes networking components:
Assign IP addresses to Pods,
Route traffic between Pods
Handle inter-node communication
Apply networking rules
Finally, the request reaches:
Application Pod
Application Pod → Serves the Request
This is where your actual application runs. The Pod processes the request and sends the response back through the same networking path.
Security & Observability → Monitors the Entire Journey
While the request travels through Kubernetes, security and monitoring tools continuously observe the traffic.
This layer helps with:
Restricting communication between services
Monitoring traffic flow Tracking latency and failures
Applying network policies
Observability and troubleshooting
This happens across all layers, not just at one specific point.
Now that we understand how traffic flows inside Kubernetes, the next obvious question is:
What tools are used at each layer, and what problem do they solve?
Deep Dive into Kubernetes Networking Tools
As we saw earlier, a request travels through different networking layers before reaching the application Pod.
Each layer has its own responsibility, and naturally, different tools are built to solve problems at those specific layers. So let’s deep dive into the tools layer by layer and understand:
What does this layer handle?
Popular Tools Available

1. Ingress/Gateway Layer:
As discussed earlier, the Ingress/Gateway Layer acts as the entry point into the Kubernetes cluster. This layer is mainly responsible for handling incoming external traffic and deciding how requests should enter and move inside the cluster.
What does this layer handle?
This layer controls:
Which application/service the request should go to
URL / Path-based routing
Authentication & Authorization
TLS / HTTPS Termination - Handling HTTPS Encryption
Rate Limiting & Traffic Filtering
Popular Tools Used in the Ingress / Gateway Layer
Ingress Controllers: NGINX Ingress Controller, HAProxy Ingress, Traefik Ingress, AWS Load Balancer Controller, Azure Application Gateway Ingress Controller
NGINX Gateway / Gateway API: Modern implementation for managing external traffic using the Kubernetes Gateway API.
Traefik: A lightweight and cloud-native ingress/gateway solution.
Cilium Gateway: Part of the Cilium ecosystem. Uses eBPF-powered networking and implements Gateway API capabilities.
Istio Gateway: Part of the Istio Service Mesh ecosystem.
2. Service Layer Tools
Once the traffic enters the cluster through the Ingress/Gateway Layer, it is forwarded to a Kubernetes Service.
But here’s the challenge: Pods in Kubernetes are temporary (ephemeral). So how does Kubernetes make sure traffic always reaches the correct Pod? This is where the Service Layer comes into play.
The Service Layer acts as the traffic manager inside the cluster and ensures requests are routed reliably to healthy application Pods.
What Does the Service Layer Handle?
Service Discovery: Services help applications find each other without hardcoding Pod IPs.
Load Balancing Across Pods: Traffic is distributed across Pods.
Service-to-Service Communication: Inside Kubernetes, services constantly communicate with each other.
Internal Traffic Encryption (mTLS): Normally, traffic inside the cluster is
Plain Text. Because TLS is often terminated at the Ingress layer. But industries like Banking, Healthcare etc may require Encrypted communication between services inside the cluster as well. This is where mTLS (Mutual TLS) becomes important.
Popular Tools Used in the Service Layer
kube-proxy: This is the default Kubernetes networking component responsible for service routing.
Istio: One of the most popular Service Mesh tools. Istio adds advanced traffic management between services.
Linkerd: A lightweight Service Mesh alternative.
Consul Service Mesh: Another Service Mesh offering. It works beyond Kubernetes as well.
Cilium Service Mesh: If you are already using Cilium, it can also provide Service Mesh capabilities without traditional sidecars.
Note: One important thing to understand is that not all tools provide the same capabilities.
For example, kube-proxy handles service routing and load balancing, but it does not provide features like mTLS (Mutual TLS), advanced traffic management, or observability.
If your requirement includes secure service-to-service communication (mTLS), traffic control, retries, or advanced visibility, you would typically need a Service Mesh like Istio, Linkerd, Consul, or solutions like Cilium Service Mesh.
The tools listed above are some of the popular options, and the right choice depends on your use case, complexity, security requirements, and operational needs.
3. Pod Networking Tools
Now the request knows which Pod it should go to. But another important question comes up:
How does Kubernetes know:
Where the Pod is?
What its IP address is?
How to route traffic across nodes?
How Pods communicate reliably?
This is where Pod Networking comes into play. Honestly, this is one of the most important layers in Kubernetes networking because:
Without Pod Networking, Pods simply cannot talk to each other.
What Does Pod Networking Handle?
Assigning IP Addresses to Pods: Every Pod gets its own IP address
Pod-to-Pod Communication: Within the same node, Across different nodes, Across namespaces without requiring NAT or complicated translations.
Cross-Node Networking: A CNI((Container Network Interface)) plugin handles the actual networking implementation.
Traffic Routing Between Nodes: This decide, how traffic moves, which node owns which pod IP range, how traffic gets routed
Network Policies: This layer can also enforce rules. Just because Pods can communicate doesn’t mean they always should. Security restrictions matter.
Popular Tools Used in Pod Networking
Flannel: One of the simplest Kubernetes networking tools. Flannel focuses mainly on Pod-to-Pod communication. This doesn't have all the above capabilities.
Calico: One of the most widely used Kubernetes networking solutions. This has Strong Network Policy support. Preferred choice in Enterprise, Prod Cluster and Security-focused environments
Cilium: Probably one of the hottest Kubernetes networking tools right now. It uses eBPF for traffic communication instead of traditional Linux Networking. Cilium is a complete ecosystem which span across all layers
AWS VPC CNI / Cloud Provider CNIs: Cloud providers also offer native networking plugins. AWS VPC CNI, Azure CNI, Google Kubernetes Engine CNI
Note: In real world Kubernetes environments, it is common to use multiple networking tools together.
For example, in cloud-managed Kubernetes services like EKS, companies often use the cloud-native CNI plugin (such as AWS VPC CNI) for Pod communication and add tools like Calico or Cilium on top for additional features such as Network Policies, security, and observability.
4. Security & Observability Tools
At this point, traffic is successfully flowing inside the cluster. Requests are reaching the correct Pods. But here comes an important question:
How do we control who can talk to whom?
How do we monitor what is happening inside the cluster?
This is where Security & Observability tools come into the picture.
This layer helps us:
Restrict communication between Pods and services
Monitor traffic flow
Debug networking problems
Understand service dependencies
Improve visibility into cluster communication
What Does This Layer Handle?
Network Policies: Who can communicate with whom
Traffic Observability: Adding detailed visibility to the network flows
Security Monitoring: Identifying unusual traffic, Policy violations etc
Popular Tools Used in This Layer
Kubernetes Network Policies: This is the native Kubernetes way to restrict Pod communication. Kubernetes Network Policies alone do not enforce anything you need compatible CNI like cilium or calico
Calico: Apart from Pod networking, Calico provides strong Network Policy enforcement, Traffic Filtering, and Security Isolation
Cilium + Hubble: Cilium takes security and observability to another level, along with many of the features offered by Calico. It provides advanced networking, security, and traffic visibility capabilities. Hubble is Cilium’s visualization tool
Istio Observability: Similar to Cilium, Istio also provides security and observability features. If you are already using Istio as your Service Mesh, you can make use of its built-in capabilities.
Conclusion
By now, you should have a better understanding of the different Kubernetes networking tools, where they fit in the networking flow, and what problem each of them is trying to solve.
Some tools help with:
Exposing applications to the outside world (Ingress / Gateway)
Service-to-service communication (Service Layer / Service Mesh)
Pod communication across nodes (CNI / Pod Networking)
Security, visibility, and traffic monitoring (Observability & Network Policies)
So the next time you hear terms like Cilium, Calico, Istio, NGINX Gateway, or Traefik, hopefully you will have a clearer idea of:
Where they fit and what their purpose is.
For a quick recap and better understanding, feel free to refer to the Flow Diagram.
I hope this blog helped simplify Kubernetes networking a little 😄
Happy Learning! 🚀
See you in the next one.